Summary
Payment tokenization is where sensitive payment data, such as credit card information, is replaced and protected by tokens. These tokens are then used to process transactions, but they are difficult to use if intercepted or stolen. Given this fact, payment tokenization serves as a vital security mechanism, helping to protect sensitive information.
What Is Payment Tokenization?
As mentioned in the summary above, payment tokenization is where sensitive payment data, such as credit card information, is replaced with tokens. For example, when a customer buys something on a website, the merchant may use a payment processor that tokenizes the customer’s primary account number (PAN).
When the same customer comes back and buys something else, the merchant can use the token to process the payment without having to handle the customer’s sensitive card data directly.
In credit card tokenization, it’s the customer’s primary account number (PAN) that gets replaced by a token.
» MORE: Data theft comes in many forms. Learn how to use credit cards safely online
What Is The Purpose of Payment Tokenization?
The purpose of payment tokenization is to improve customer data security by ensuring that sensitive payment information is not transmitted or stored. This makes it more difficult for malicious actors to copy bank and payment information.
Why Is Tokenization Important For Online Merchants?
Tokenization is crucial for online merchants for a number of reasons.
Enhanced Security
Tokenization significantly reduces the risk of sensitive data being intercepted or stolen because actual payment details are not stored or transmitted during transactions.
Risk Mitigation
In the event of a data breach, the damage is much less severe if payment data has been tokenized. Instead of stealing actual card numbers, hackers would only obtain useless tokens.
Customer Trust
Consumers are more likely to shop with merchants they believe are taking appropriate steps to protect their personal information.
Tokenization is a step in this direction.
Simplified Transactions
Once a customer’s payment information is tokenized, the token can be used for future transactions. This means the customer doesn’t have to enter their card details each time they make a purchase.
Regulatory Compliance
Many industries have strict regulations regarding the handling and storage of sensitive data. The Payment Card Industry Data Security Standard (PCI DSS), for instance, applies to companies that accept card payments.
Tokenization can help businesses meet these requirements by reducing the amount of sensitive data they handle.
» MORE: What is PCI compliance?
How Does Payment Tokenization Work?
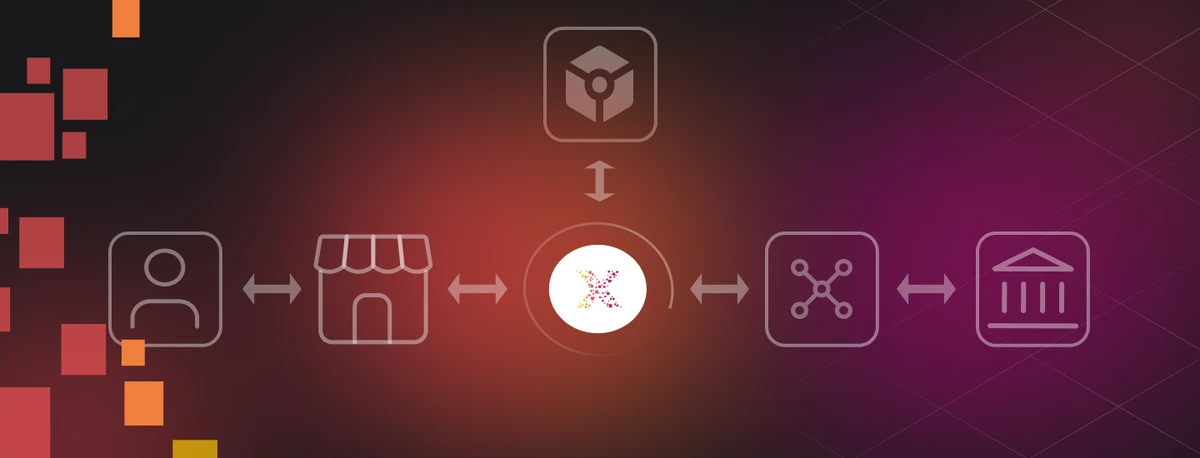
While payment tokenization has several moving parts, the process is automated and occurs in real-time, adding an important layer of security to digital transactions.
The tokenization process begins when your credit card number (Primary Account Number) is used to create a unique ‘token.’
The token can only work in certain places or situations, which are called predefined domains or payment environments.
This means the token is designed to be used only where it’s supposed to be used, making it even more secure. It’s like having a key that can only open one specific door and no other, keeping your information safer.
Let’s examine what this would look like in a real-world example:
1. Initial Purchase
A customer initiates a transaction and provides their payment information.
2. Token Generation
The platform, such as a payment gateway, takes this information and generates an alphanumeric ID, or “token,” from the customer’s PAN.
3. Token Encryption
The newly generated token is encrypted and sent over to the merchant’s payment processor. The actual payment data, including the PAN, remains securely stored within the payment gateway or a secure token vault. It does not travel with the transaction, thereby preserving its security.
4. Payment Processing
The merchant’s payment provider receives the encrypted token and re-encrypts it before sending it along to the Automated Clearing House (ACH) network. This double layer of encryption further ensures the safety of the transaction.
5. Transaction Confirmation
Upon receiving authorization from the ACH network, a confirmation is sent back through the chain. The payment is processed, and the transaction is completed.
Throughout this entire process, the customer’s actual payment details are never exposed, thereby ensuring the highest level of security.
» MORE: How to respond to a dangerous cardholder data breach
Payment Tokenization and Mobile Wallets
Another practical example of payment tokenization is the use of mobile wallet applications like Apple Pay, Google Pay, or Samsung Pay. Here’s how payment tokenization works in that context.
1. Adding a Card
When you add a credit or debit card to one of these mobile wallet apps, your card information is sent to the card issuer or network.
2. Token Generation
The card issuer or network replaces your card information with a device-specific token. This token, alongside a transaction-specific dynamic security code, is stored on your device.
3. Making a Purchase
When you make a purchase using Apple Pay, Google Pay, or Samsung Pay, the payment is processed with the token and security code. Your actual card number is not shared with the merchant or sent with the payment, and the dynamic security code changes with every transaction.
4. Transaction Verification
The token and security code are sent to your card network for verification. The network confirms that the token corresponds to your actual card number and that the dynamic security code for the transaction is correct.
5. Payment Confirmation
Once everything checks out, the transaction is approved, and the payment goes through. At no point during the transaction does the merchant have access to your actual card details.
» MORE: 9 alternative payment methods you can use, including mobile wallets
What Are The Benefits of Payment Tokenization?
In addition to the benefits already mentioned, payment tokenization allows for the following.
Global Payments
Tokenization enables safer cross-border transactions, as tokens can be used irrespective of geographical location.
Cross-Channel Consistency
The same tokenized payment data can be used across different sales channels (online, in-store, mobile), creating a more consistent and convenient shopping experience.
Note that cross-channel usage depends on the specific tokenization system in place. Not all businesses or systems may support this.
Supports Multiple Payment Methods
Tokenization isn’t limited to credit or debit cards. It can be used to protect various types of payment methods, including mobile wallets.
Fraud Monitoring and Analysis
Tokens can be used in fraud detection systems to analyze purchasing patterns and identify unusual behavior without exposing actual cardholder data.
Cost Savings
Decreasing the risk of data breaches (which can lead to hefty fines, remediation costs, and reputational damage) means fewer costs for businesses.
Data Storage for Payment Disputes
Tokenization allows businesses to keep customers’ payment information on hand. This stored information can be used later for things like refunds, repeat payments, and handling payment disagreements (chargebacks).
For example, in a situation where a customer initiates a chargeback, saying they didn’t authorize a certain transaction, the tokenized data can help the merchant verify the transaction details.
Since the token is unique to the specific transaction and payment method, it serves as proof of whether the transaction took place or not.
Data Management
Tokenization can help reduce the quantity of sensitive data that a company needs to manage.
Reduced Scope of Audits
Since tokenization minimizes the amount of sensitive data stored, it also reduces the scope of IT environments that auditors need to review, leading to potentially quicker and less expensive audits.
» MORE: The benefits of choosing Pixxles
What Are The Disadvantages of Payment Tokenization?
While payment tokenization offers numerous advantages, there are also some potential disadvantages to consider.
Implementation Cost
The initial setup of a tokenization system can be expensive, especially for small businesses.
These costs may include the purchase of software or hardware, as well as hiring technical expertise to implement and manage the system.
System Compatibility
Not all systems are designed to handle tokenization. If a business has legacy systems or uses third-party vendors, there might be compatibility issues.
Token Management
While tokens are designed to reduce the risk of handling sensitive data, they themselves must be securely managed.
Potential for Decryption
While tokenization is a robust security method, no system is entirely immune to sophisticated cyber attacks. If an attacker gains access to the tokenization system, they may be able to reverse-engineer the tokenization process.
Vendor Dependence
If a business uses a third-party vendor for tokenization, they become dependent on that vendor’s stability and security. If the vendor goes out of business or suffers a security breach, it could impact the business.
Maintenance and Updates
Like all technology-based solutions, a tokenization system requires regular updates and maintenance to remain secure and effective.
Tokenization vs. Encryption – How Is Tokenization Different Than Encryption?
While both tokenization and encryption are used to protect sensitive data, they work in fundamentally different ways.
Tokenization
Tokenization replaces sensitive data with non-sensitive substitutes. The original data is stored in a secure lookup table or “token vault,” and each token maps back to the original data.
Importantly, there’s no mathematical algorithm that can reverse a token back into the original data; the only way to retrieve the original data is to access the secure token vault with the correct permissions.
This means that even if a token is intercepted, it’s of no use without access to the token vault.
Encryption
Encryption, on the other hand, transforms sensitive data into a different format using an algorithm. The original data (plaintext) is converted into encrypted data (ciphertext) using an encryption key.
The process can be reversed (decrypted) to retrieve the original data, given the correct decryption key.
History of Credit Card Tokenization
The concept of tokenization is not new. However, the application of tokenization to credit card data is a relatively recent development, coming into prominence in the late 2000s and early 2010s.
As ecommerce popularized in the late 1990s and early 2000s, so did the rate of credit card fraud. Digital transactions provided new opportunities for fraudsters to intercept sensitive credit card data, leading to a rapid increase in data breaches.
In response, the major credit card brands introduced the Payment Card Industry Data Security Standard (PCI DSS) in 2004, establishing guidelines for businesses to secure cardholder data.
Around this time, tokenization began to be applied to credit card payment information.
Today, payment tokenization is supported by major credit card networks and used by businesses worldwide to secure their payment processes. Mobile payment solutions like Apple Pay and Google Pay also use tokenization technology to ensure secure transactions.